Some of you may remember my patchless AMSI bypass article and how it was used inside SharpBlock to bypass AMSI on the child process that SharpBlock spawns. This is all well a good when up against client environments that are not too sensitive to the fork and run post exploitation model of operating. What about […]
Merging C# Assemblies using dnMerge
Introduction When it comes to automating builds for any project that I undertake, my goto OS is usually Linux. Generally I find the deployment of build nodes easier to deploy and manage and usually cheaper than their Windows counterparts. The problem with this of course is Windows based software generally needs cross-compiling in someway or […]

Attacking Smart Card Based Active Directory Networks
Introduction Recently I was involved in an engagement where I was attacking smart card based Active Directory networks. The fact is though, you don’t need a physical smart card at all to authenticate to Active Directory that enforces smart card logon. The attributes of the certificate determine if it can be used for smart card […]
Lets Create An EDR… And Bypass It! Part 2
A 2 part series on creating a basic EDR detection system and then a bypass implementation. In part 2 I introduce SharpBlock, a method of bypassing EDR’s.
Lets Create An EDR… And Bypass It! Part 1
A 2 part series on creating a basic EDR detection system and then a bypass implementation. In part one we cover how to create a basic EDR.
SweetPotato – Local Service to SYSTEM
Upgraded JuicyPotato performing Local Service to SYSTEM privilege escalation on Windows 7 to the latest Windows 10 / Server 2019.

Lenovo CVE-2020-8319 and CVE-2020-8324 PoC
C# PoC for Lenovo CVE-2020-8319 and CVE-2020-8324
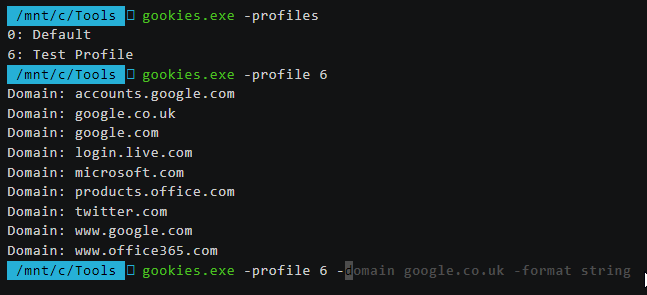
Gookies : A Chrome cookie dumper
A Chrome cookie decryptor and dumping tool

Weaponizing your favorite Go program for Cobalt Strike
How to convert a Go program to a reflective DLL for Cobalt Strike